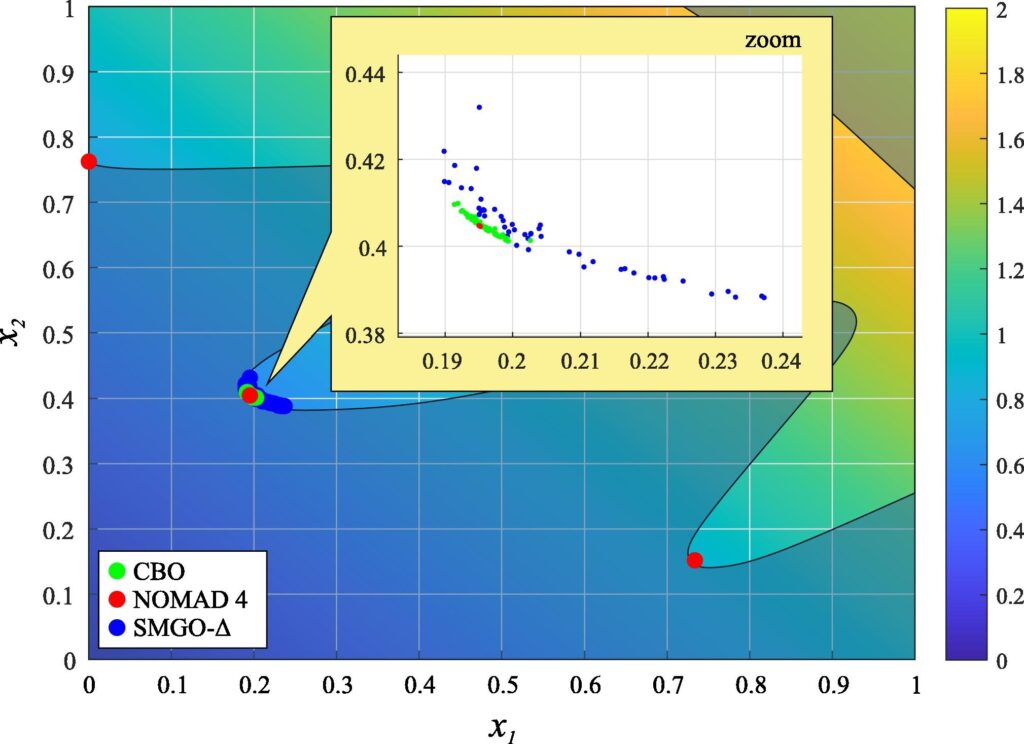
An open access paper published in Information Sciences describes SMGO-Δ, a novel global optimization algorithm.
Rooted in Set Membership theory, it builds surrogate models of black-box cost and constraint functions and decides whether to explore or exploit depending on function uncertainty and estimated constraint violations. The user can choose whether to have a more aggressive or a more cautious behavior by tuning just one parameter.
The Matlab code is also available here for anyone to use it!
